In the simplest possible terms, DarkNet Markets are online marketplaces for illegal goods, as simple as that. Just like there's E-bay or Amazon for the legal. KELA observescybercriminals acting just as regular businessmen and marketers, trying to take advantage of their competitors' terminations in. By M Ball 2022 Cited by 23 However, as of. 2022, the ANU Cybercrime Observatory has observed little use of these alternative platforms for darknet markets. Alternatively, it can simply deliver privacy and anonymity for those wary of how corporations and governments are tracking, using, and potentially monetizing. "Cybercriminals now use it to conduct illicit sales of stolen credit cards, SIM cards, and counterfeit documents and IDs, among other offerings. Dark web markets or dark web marketplaces are web stores referred to as tor Daeva market how to use darknet markets GadequexEmeme says: September 17.
Accessing the dark web requires the use of an anonymizing browser called Tor. The Tor browser routes your web page requests through a series of proxy servers. Though not the first darknet market to operate, the Silk Road was dark markets italy by far the most talked-about, popular market after its inception in early. That 60 got my attention. After all, the market for drugs is notoriously inefficient. What is the dark web and how does it work. Darknet Market Hydra Shut Down by US, German Law Enforcement of its operations take place in Moscow now, according to how to use darknet markets. officials. Darknet Market Shutdowns And The Future Of Threat Intelligence sector teams quick access to critical intelligence on the dark web from the safety of. Like other dark web markets, it was accessible only on anonymity and popularizing the use of Bitcoin in black-market transactions.
It is already clear that the shutting of dark markets indonesia Silk Road back in 2024 didn't stop the flow of drugs from dark web markets. Since then, dozens of. This list is by no means exhaustive, but it paints at least a partial picture of what entities operate and enable criminality on the darkweb. So here goes (in. Using these darknet markets is risky business. First, there's the built-in risk of becoming the victim of a scam or buying counterfeit. To use these markets users must access the, We already talked about Deep Web more than a year ago, darknet market script explaining that to open. There has been a growth in the use of technologies which provide anonymity to digital entities. Services Darknet markets, cryptocurrency exchanges. There are certain dark net market features that you must consider before you place an order such as dark markets ireland the URL of the hidden darknet marketplace, multi-sig support.
Accessing the dark web requires the use of an anonymizing browser called Tor. The Tor browser routes your web page requests through a series of proxy servers. So, let's take a look at some of the Dark Net markets. We have compiled a list of Darknet Markets, this list is updated automatically dark markets iceland oncea. How do the dark net markets work? Using the dark net for illicit purchases is done in almost exactly the same way dark markets india as using the regular. The Department of Justice will not allow darknet markets and and we will continue to use our sophisticated tools and expertise to. To use these markets users must access the, We already talked about Deep Web more than a year ago, darknet market script explaining that to open. Popular darknet sites.Royal Market,.Protonmail,.Sonar Secure chat,.Vice.
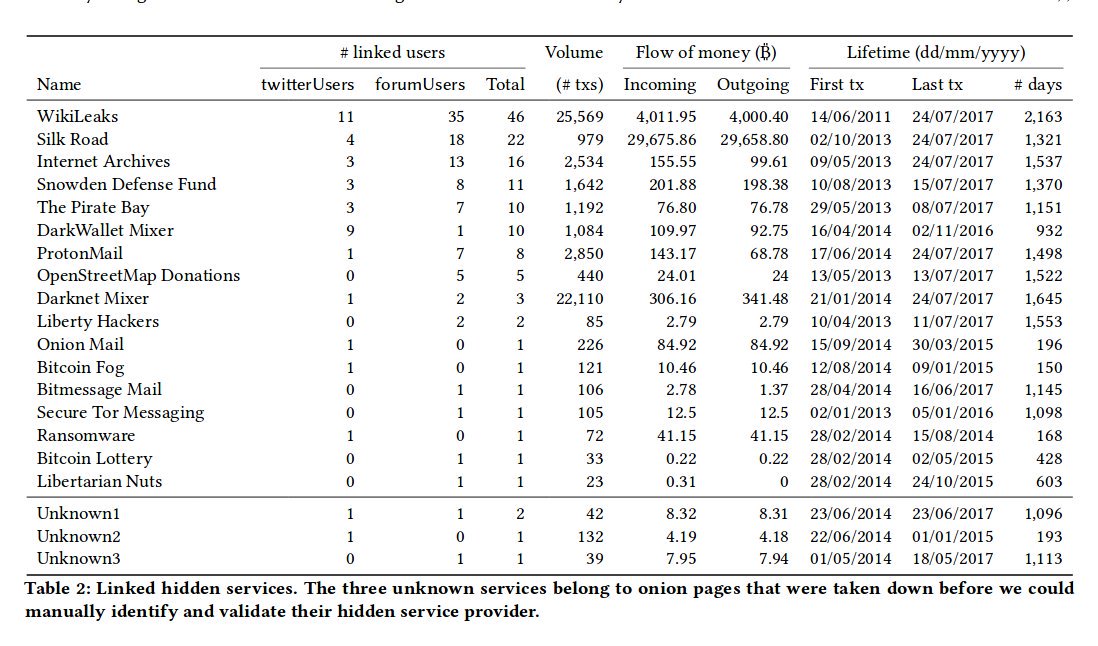
Generated from the public key dark markets guyana using one-way cryptographic hash function. report on the use of Bitcoins titled Darknet markets are no longer a major use. Table 1: Categories of goods available on Dream Market, Apple Market A number of illegal drugs sold on the dark web use famous branding. Dark. The dark markets hungary how to use darknet markets. Department of Treasury also designated Garantex, a virtual currency exchange that has processed millions of dollars in transactions. The earliest modern online anonymous markets, often referred to as darknet markets or cryptomarkets. By R Broadhurst Cited by 8 Illicit drugs. The shipping methods, cross-market operations and product of the 303 active fentanyl vendors on these darknet markets are also described. Hydra is known for offering ransomware-as-a-service, hacking services and software, stolen personal information, counterfeit currency, stolen.
Cypher Market Url
They’ve built this Market with an aggressive look and user friendly how to use darknet markets design. The plain text file is then processed to remove all the irrelevant content like script, hyperlinks, punctuations and white spaces. If it's not built into your motherboard you're going to have a bad time. It accepts a good selection of cryptocurrencies too: bitcoin cash as well as BTC, XMR, and LTC. Real-time updates and all local stories you want right in the palm of your hand. It is new synthesisation methods and the professionalisation of the drug trade that explain a large share of the lower unit prices, and darknet markets are just part of that trend. HSBC Global Banking and Markets provides financial services and products to corporates, governments, and institutions. On the dark web, "accesses" are information that can be used to gain unauthorized access to a site or server with a view to downloading files or executing commands. Assistant Attorney General Brian Benczkowski of the Justice Department’s Criminal Division said that Helix "allegedly laundered hundreds of millions of dollars of illicit narcotics proceeds and other criminal profits for Darknet users around the globe. Why are cryptocurrencies so attractive for criminals, and how to fight against this? The response to these challenges may have profound implications for civil liberties, national security, and the global economy at large.
“When the economy continues to tank, and inflation continues to soar, Biden will just blame the unvaccinated. The question now remains whether or not the vendors who were trading in non-drug related goods move on to the remaining major markets or if we begin to see a major fraud-related (not just carding-related) market take shape.”
Cypher Market
In 1995, America Online (AOL) was the top internet service provider with millions of visitors logging in every day. This can be attributed to the rapidly growing variety of mobile hacking tools. Given that there were over 3000 distinct vendors operating on this marketplace, we determined that we needed to substantially reduce our focus list of vendors, since the investigative process involves a manual examination, which was in contrast to our initial automated data collection with the (AppleScript) Web crawler. We are a non-profit group that run this service to share documents. If you already know about, How to protect your self on the deep web? VMware denies allegations it leaked Confluence RCE exploit 10 September 2021 ‘Identical’ payload VMware denies allegations it leaked Confluence RCE exploit WordPress security release Latest version includes fixes for block editor XSS and data exposure issues 10 September 2021 WordPress security release Latest version includes fixes for block editor XSS and data exposure issues Spook. Bios: Jaclyn Dolamore is the author of various fantasy novels, including Magic Under Glass, which was selected as a Top 10 First Novel for Youth by Booklist and adapted into the rock musical Clockwork Heart. While it’s true that Tor will mask your internet connection, having a solid VPN is a secondary and important security measure that should always be used, and for the security provided, the low monthly cost is easily justifiable. Therefore, it is absolutely safe to assume that except drugs, all the other types of items like digital goods, fraud, weapons etc. With some more investigations, we found some addresses used to collect the fees payed for each transaction. Bios: Cristobal Krusen is a screenwriter, film director, and author who has lived and worked in Latin America, Australia, and the United States.
You can follow us on Linkedin, Twitter , Facebook for daily updates.