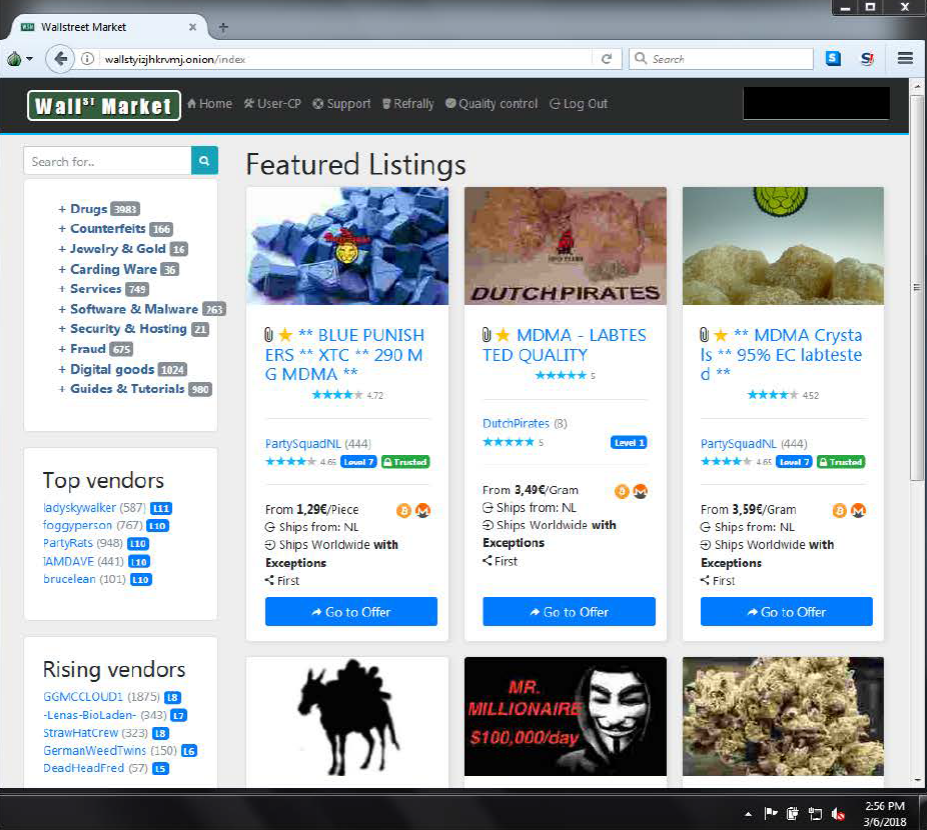
Then, you can begin to browse the dark web. The next step is to download and install Windows Expert bundle as well as set up yourtorrc file. Today, the use of TOR (The Onion Router, technology that anonymizes your web activity), obscured URLs and encryption provide the foundations of. A spider is essentially a special software robot that searches a website page returning to the search engine with information that is contained. What we do know for certain, is that for everyday use, we access only 10 percent of the internet. The websites that we visit daily belong to the. The number of live, accessible .onion sites amounts to less than dark web sites of surface web domains, researchers report. The dark web has a shady reputation. Hidden below the transparency and visibility of the internet's surface, the complex anonymity networks.
If you can take appropriate safety and security measures, there are several valid business reasons a legal researcher would have for. This tutorial explains every aspect of the darkfox market Dark Web, how to get on the dark websites and the precautions you must take while accessing them. Although Dark Web sites are frequently changing or disappearing, and determining the URL is Attackers Hacked 6,500 Daniel's Hosting Dark Web Websites. Follow our step-by-step guide on how to access the dark web using the Tor browser and discover everything you need to know about navigating. To compare apples-2-apples we will search for The dark web refers to sites that are not indexed and only accessible via specialized web browsers. You will come across Tor Browser every time you look for deep web information. It is the most powerful Deep Web browser and with the highest.
The dark web has a shady reputation. Hidden below the transparency and visibility of the internet's surface, the complex anonymity networks. That's why criminals, terrorists, and others conduct illegal darkfox market url business there. If your identity were stolen by a cyber criminal, chances are that. Once inside the dark web, dark net markets exist that sell sensitive data stolen in breaches (in addition to illegal products like drugs and. Each computer uses a unique name during this communication. That name is an IP address (IP stands for Internet Protocol, it is formatted like. The dark web is a decentralized network of internet sites that try to make users as anonymous as possible by routing all their. Dark Web is a part or division of the Deep web which is intentionally hidden from normal search engines. All its data is encrypted.
Dark mode for all websites in Chrome browser with opportunity to exclude any domain or create custom theme. Better darkfox market link understand what dark web is, how it's used & why dark web is primarily associated with ransomware attacks & data breaches. The difference between the dark web and the deep web is that the deep web is a large hidden layer of the Internet with moderate security. Dork net. This site will let you find the links to other sites and places you might want to visit on the darknet exactly what search engines do. The dark web and deep web may be related but differ greatly. So what exactly are they, and why are technology reporters so darkfox market darknet wary when using. Words of Caution When Using Dark Web Sites.
The deep web also is inaccessible by search engine, but it's largely composed of sites and content that aren't public for reasons like paywalls. Here are some of the creepiest websites on the internet, from odd animation to weird to documenting supremely strange dark web sites things. Check out these super scary. As one of Canada's top business law firms, Blake, Cassels & Graydon LLP (Blakes) provides exceptional legal services to leading businesses. The dark web and deep web may be related but differ greatly. So what exactly are they, and why are technology reporters so wary when using. The dark web is the part of the web you can only access with a special browser, like Tor. Here you'll find 20 dark web sites worth visiting. Visual Inspiration: 30 Beautiful Dark Web Designs. Table of Contents. 1. Weyland dark web sites. dark web sites. dark web sites. Jack Daniel's.
Dark Markets Norway
US Coast Guard Cutter James (WMSL 754) is receiving the award in the Detection & Monitoring category for their unprecedented 11 days of tactical control while JIATF South was shutdown for Hurricane IRMA. Mutual funds are managed by dark web sites investment management experts whose job is to allocate the fund’s assets to produce strong investment returns for the fund’s investors. RTM is usually released before the general availability (GA) version is released to the public. Similar to a Denial-of-Service (DoS) attack, a Distributed Denial-of-Service (DDoS) attack is a type of malicious network offensive conducted by a number of systems against a target. If there is a set of inventory with strong demand but the product is deemed to be of higher quality there is premium on that product. Some may argue about phishing, but I know DeepDotWeb's list has not hosted a phishing link. Indexing can be used to track and group different data sets from a large number of topics. In April when Grams was launched Bitcoin was around US$500 and now is at US$380. RIAs must be registered on a state level and with the Securities and Exchange Commission (SEC) in order to prove their qualifications and expertise.
“If there's something shady going on online, chances are it's happening on the dark web.”
Dark Markets Paraguay
There are lots of perfectly legitimate reasons you might want to access all that shady content. Worldwide, the category saw annual revenues in excess of US $400 billion in 2020, up by more than 40 percent compared to the previous year. Ramnath Kumar, Shweta Yadav, Raminta Daniulaityte, Francois Lamy, Krishnaprasad Thirunarayan, Usha Lokala, and Amit Sheth. Gas was built into the system to allocate resources to the network of miners darkc0de who dark web sites validate transactions and create new blocks. The major risk in it is that the market can always run away with the money defrauding you. On the security front too provides for 2-factor authentications, PGP encryption and Escrow.
You can follow us on Linkedin, Twitter , Facebook for daily updates.